Keystroke Logging: Capturing user’s keystroke entries to acquire confidential specifics including passwords or personal details.In the course of this essential stage, the intruder utilizes the weaknesses recognized through scanning for unauthorized entry in to the concentrate on procedure. This will require leveraging applications, working units,
 Michael Bower Then & Now!
Michael Bower Then & Now!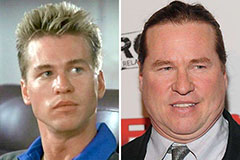 Val Kilmer Then & Now!
Val Kilmer Then & Now! Lucy Lawless Then & Now!
Lucy Lawless Then & Now! Jane Carrey Then & Now!
Jane Carrey Then & Now! The Olsen Twins Then & Now!
The Olsen Twins Then & Now!